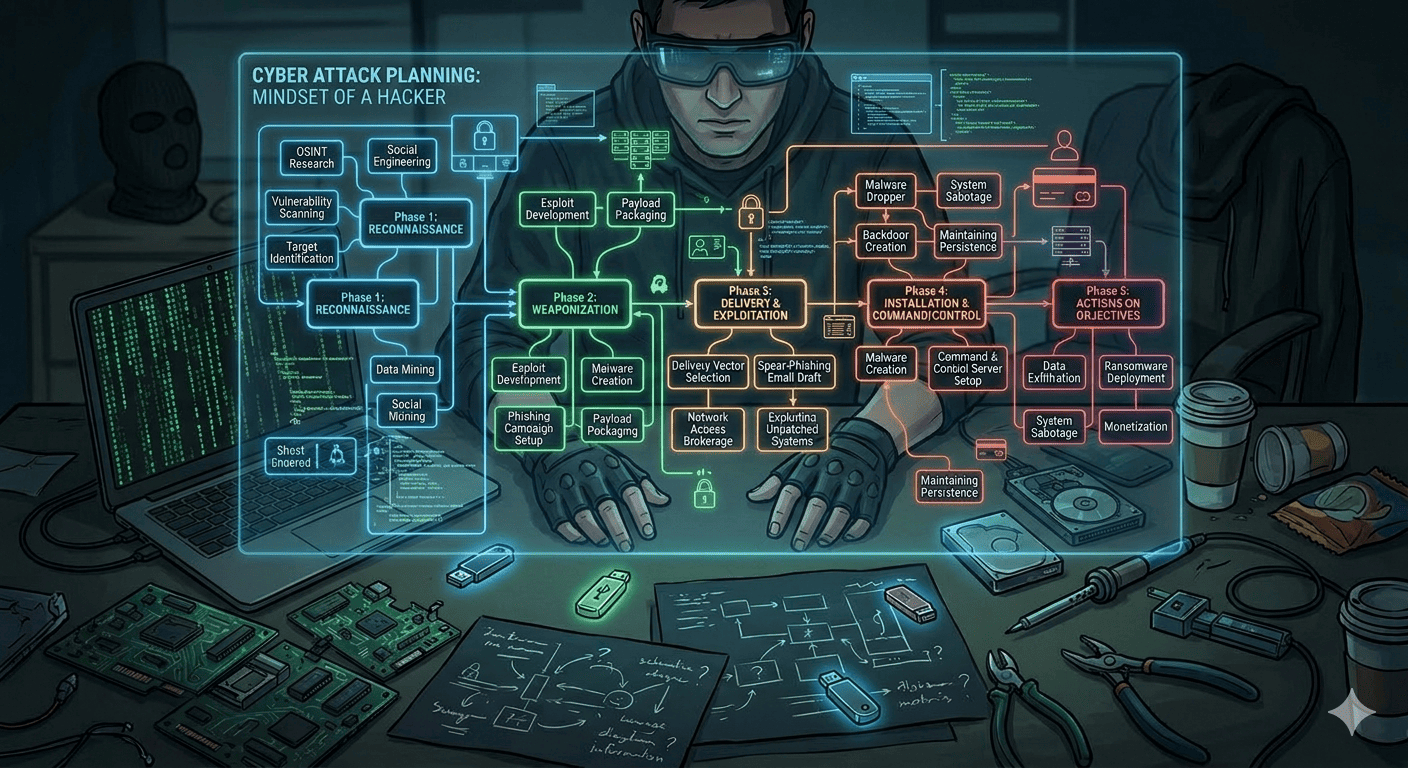
Cybercrime has emerged as one of the biggest dangers in the digital age. From small-scale businesses to multinational companies, businesses are regularly attacked by cybercriminals seeking to snare data, disrupt services or even gain financial gain. Knowing how Criminals Plan Cyber Attacks is crucial for companies as well as individuals looking to secure their systems and data. Cybercriminals don’t attack systems randomly. Instead, they employ an established process of conducting research, planning, testing vulnerabilities, and carrying out sophisticated attacks. This article
Cyberattacks today are no longer random or noisy. Modern attackers plan carefully, move silently, and target high-value systems and data. Traditional security testing often fails to show how attackers behave in the real world. This is why Red Teaming in Cybersecurity has become a critical part of advanced security programs. Red Teaming helps organizations understand how a real attacker could compromise their environment, how long it would take, and whether security teams would detect the
Cloud computing has become the default choice for businesses of all sizes. From startups to large enterprises, organizations rely on AWS, Microsoft Azure, and Google Cloud to run applications, store data, and scale faster than ever before. While cloud platforms offer powerful security features, cloud security breaches are still happening frequently and at scale. Most of these incidents are not caused by advanced hacking techniques. They happen because of misconfigurations, weak access controls, exposed services,
Cybersecurity threats are growing in both scale and sophistication. From ransomware campaigns and data breaches to supply chain attacks, organizations across industries are under constant pressure to protect their digital assets. As reliance on digital infrastructure increases, the demand for VAPT Services in India has grown significantly, helping organizations proactively identify and address security weaknesses. Among the most dangerous cybersecurity threats are zero day vulnerability, security flaws that attackers exploit before vendors or security teams
Cyberattacks no longer target only large enterprises; startups, SaaS companies, healthcare providers, and e-commerce platforms are equally at risk. Applications are released faster, infrastructure is more complex, and attackers use automation to exploit known flaws within minutes. Traditional security controls like firewalls and antivirus are necessary, but they cannot reveal real, exploitable weaknesses in your applications and networks. This is where VAPT testing india becomes critical. By combining systematic vulnerability discovery with real-world exploitation, penetration